Boingo HotSpot security loophole
URL hacking to get unlimited Wi-Fi at a Boingo HotSpot at JFK.
TL;DR: showing how you can tweak the URL to get unlimited Wi-Fi at a Boingo HotSpot at John F. Kennedy International Airport.
WHY
So I was in the US recently for an internship interview, and was travelling back home to Montreal from NYC. I was waiting for my flight at JFK, where American Airlines had just announced that my flight was delayed by 2 hours.
Mildly disgruntled by this, I logged onto JFK’s Boingo HotSpot Wi-Fi, free for (ostensibly) 30 minutes. This seemed too short, which got me wondering (I blame my aforementioned grumpiness) - how do they keep track of user identity? MAC spoofing is often used to get around paid/limited Wi-Fi connections.
But getting around Boingo HotSpot’s paywall interestingly wasn’t even as involved as that. Thing is, URLs are fun to play around with - this is how PrettyPrintGmail works, for example. Too many websites trust URLs too much. And Boingo takes this laziness to a whole new level.
HOW
When I conect to the Boingo Wi-Fi router, I get a sign-in page with this URL: https://portal.boingohotspot.net/jfk.t8/welcome?blahblahblah. I noticed the /jfk.t8/ (I was at Terminal 8). (How) Are they validating that I’m actually at JFK T8? If I could log on to a different Boingo hotspot at some other airport (and there are several), I could get unlimited free Wi-Fi minutes, simply by cycling through airports. The Boingo server should check if a request for a particular’s airport’s sign-in page was actually made from the router(s) at that location. So if I wanted to sign in to access Wi-Fi at say the Buffalo portal login, they would make sure I was in Buffalo at the time – right? Or something smarter than that? Surely?
Nope. This is what I did:
-
Went to
https://portal.boingohotspot.net(stripped the terminal + session information out, in other words). -
Got this page:
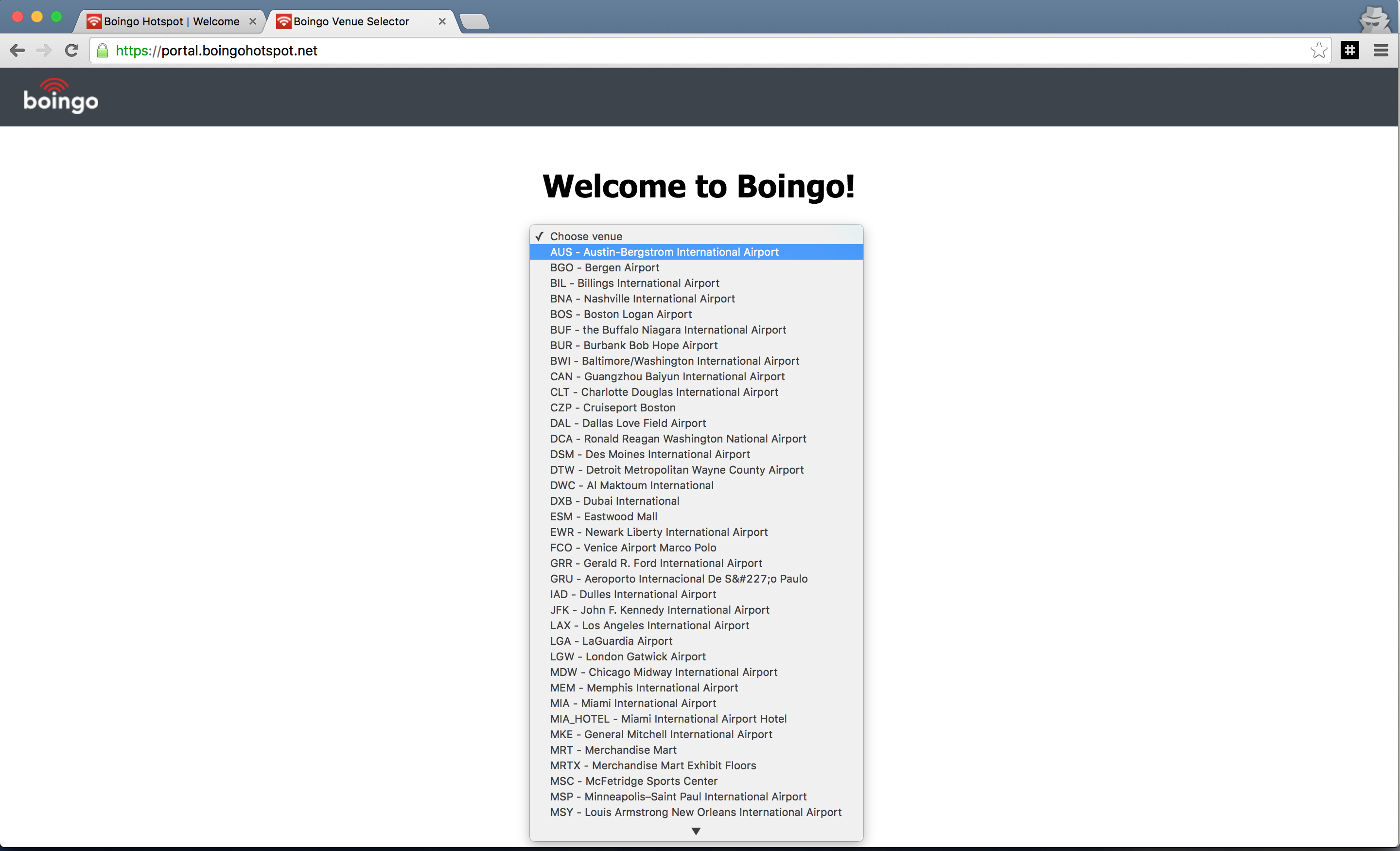
- Claimed I was in Dallas:
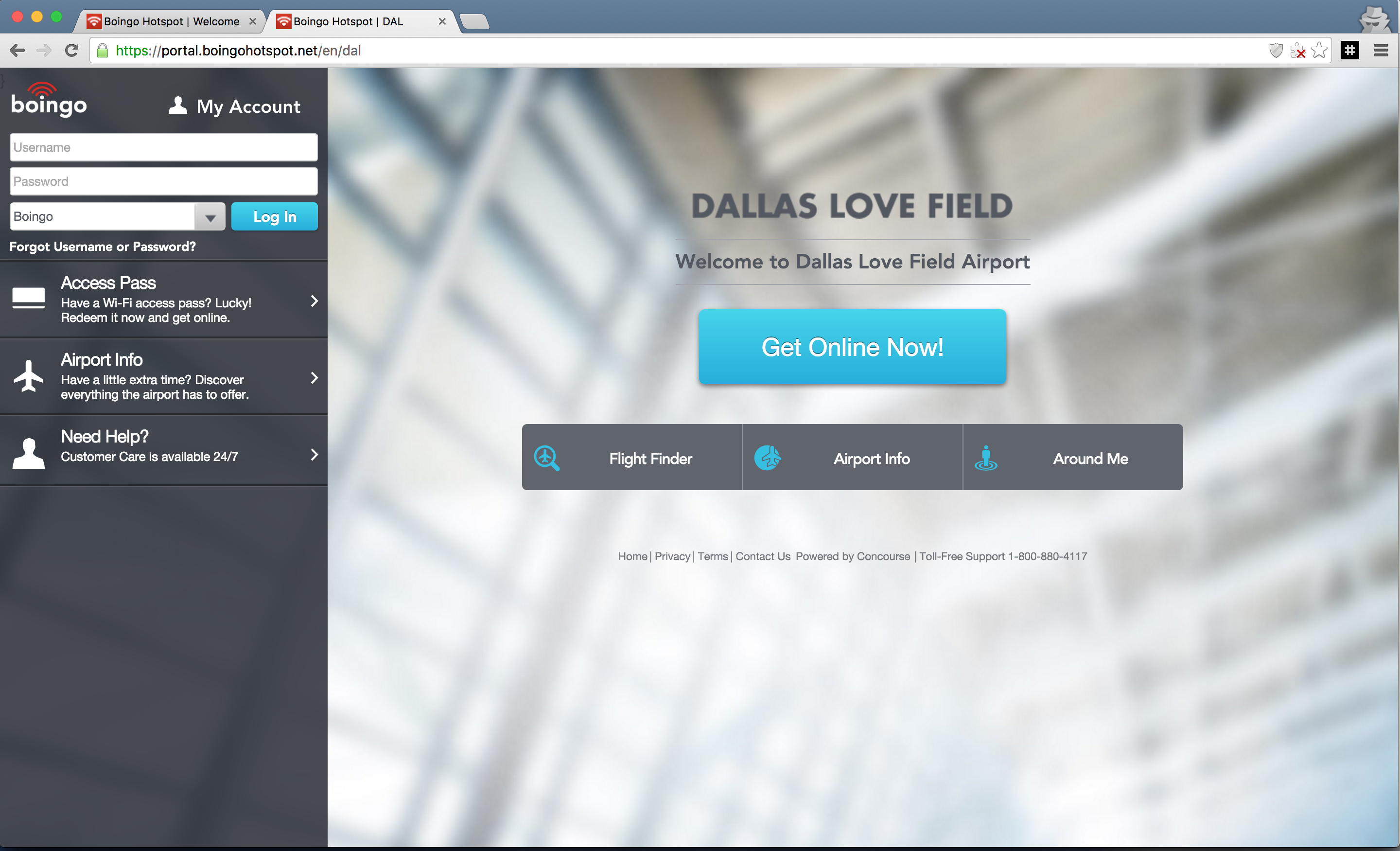
- They believed me:
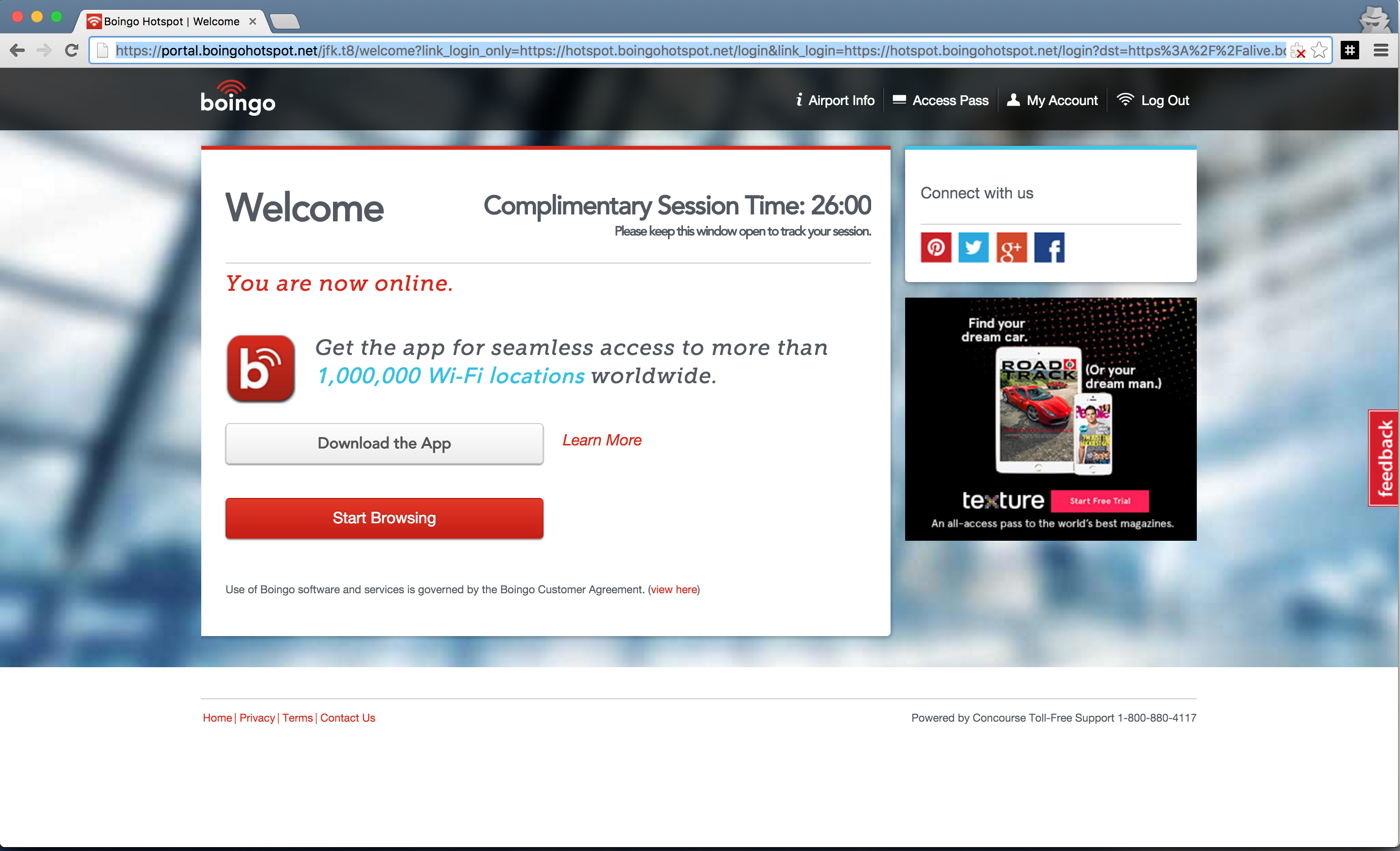
- Signed up for free Wi-Fi.
I did this a couple of times. Some airports give you a ton of free minutes - Austin-Bergstrom International airport for example gave me an hour and a half. Most give you around 30 minutes. I was able to cycle through a couple of these airports before it came time for me to board.
NOTE: I used an Incognito Window for signing into the Boingo hotspot. I forgot to test what would have happened if I my cookies were available.
Exploiting Boingo hotspots seems to be nothing new - there are tons of posts all over the internet about how you can spoof your MAC, or navigate to a Boingo partner website and use that as a gateway, or just set window.location.href using web devtools instead of entering a URL in the address bar. Those are fairly hacky approaches though, I believe. I mean, anyone could think of going to the original Boingo domain and changing their geographical location. Shoddy engineering on their part.
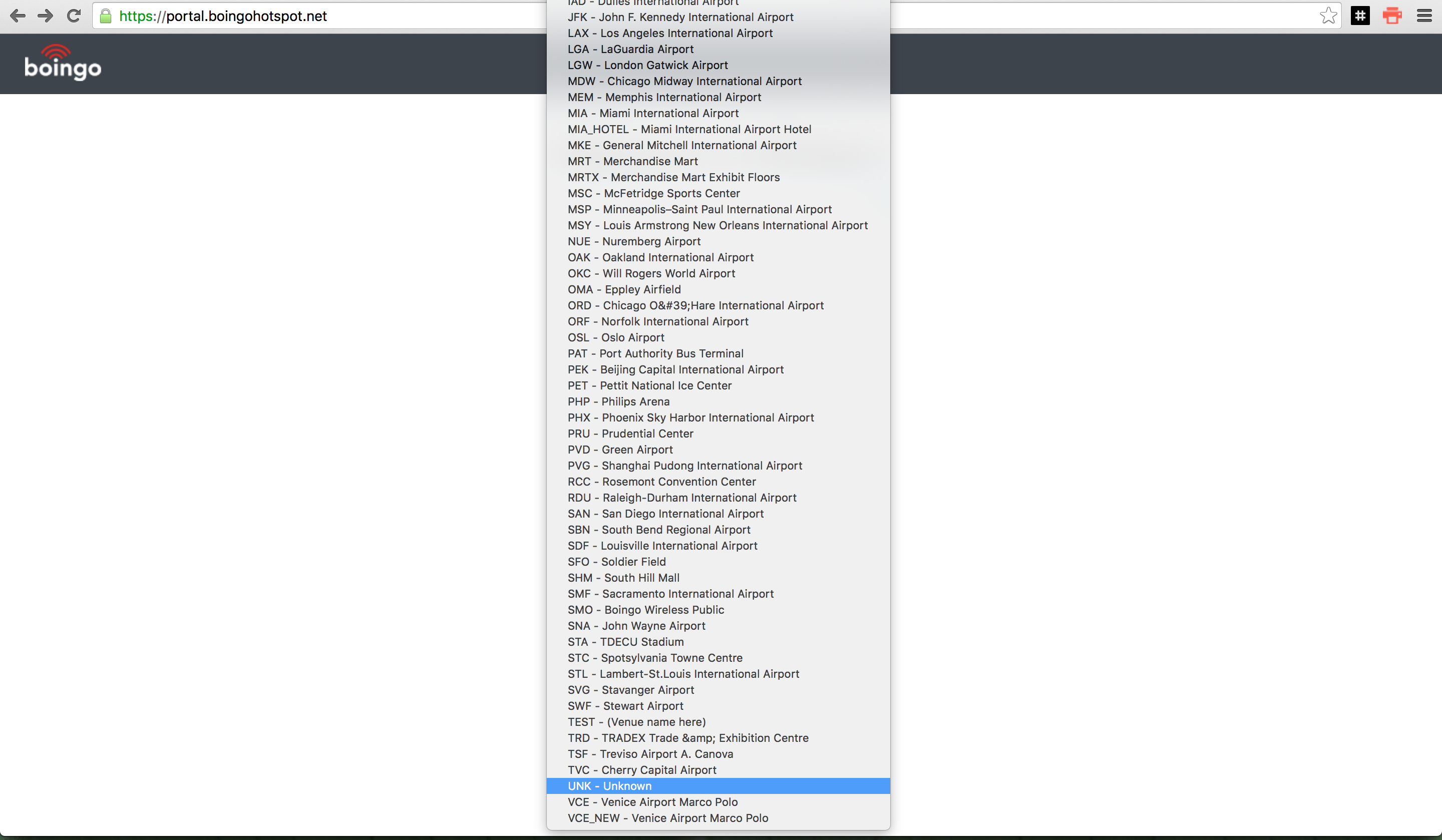
EDIT: There also seems to be an ‘Unknown’ airport, which seems to give unlimited free Wi-Fi. Could someone check?
UPDATE: It seems that https://portal.boingohotspot.net sometimes redirects to boingo.com. To get around this, simply go to https://portal.boingohotspot.net/unk (directly to the UNKNOWN airport, in other words).